Syhunt Community Edition Released
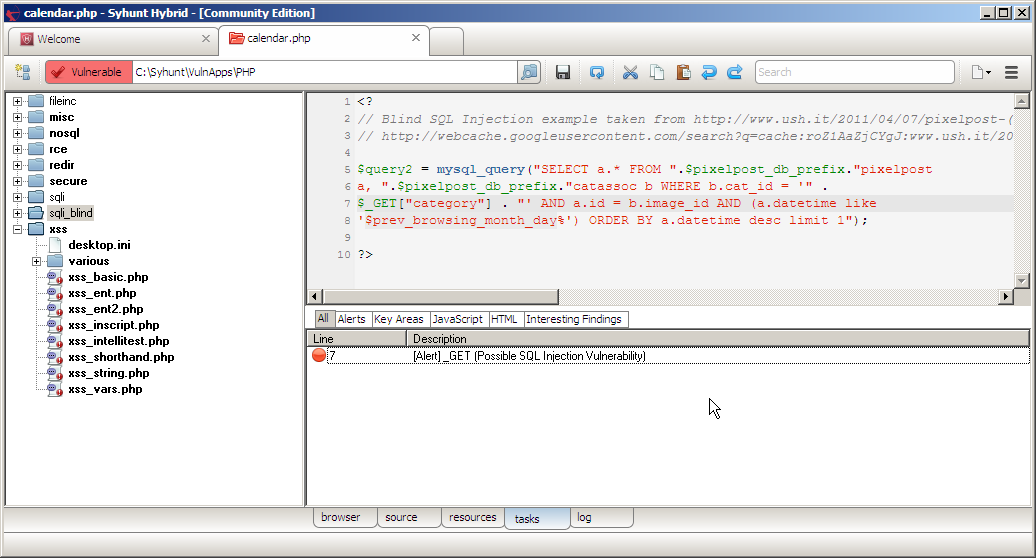
Today we made available the Community Edition for our hybrid application security scanner. This is the first release of a free edition of our flagship product Syhunt Hybrid, which now can be used at no charge by the community.
It can help security auditors, security professionals, developers and hackers to start improving the security of web applications and websites right away, helping evaluate the coding practices currently in place within an organization or a group.
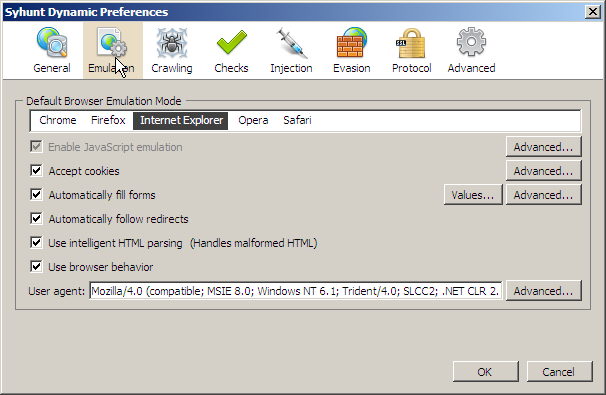
With this version you are now able to scan and detect the following vulnerabilities, including commonly exploited coding mistakes, through both dynamic and source code analysis:
- Cross-Site Scripting (XSS)
- SQL Injection (for MySQL and Oracle powered web applications)
- Unvalidated Redirects
- Directory Listing
- Directory Traversal
- Information Disclosure
- Old/Backup Files (Common Backup Files & Folders)
- Path Disclosure
- Source Code Disclosure
Syhunt Community Edition runs under any modern Windows version and can be downloaded at the link below. Feel free to try it and share your feedback and suggestions.
Download Syhunt Community 5.3
MD5 : 189b5e3ba8c754130891749a99d01b54
SHA-1: cbb24a0b37d187a373ee3fa792d76225327dbd16
Labels: Community, Free Tools, Syhunt Community Edition, Vulnerabilities, Web Application Security Scanner




